Most Commented
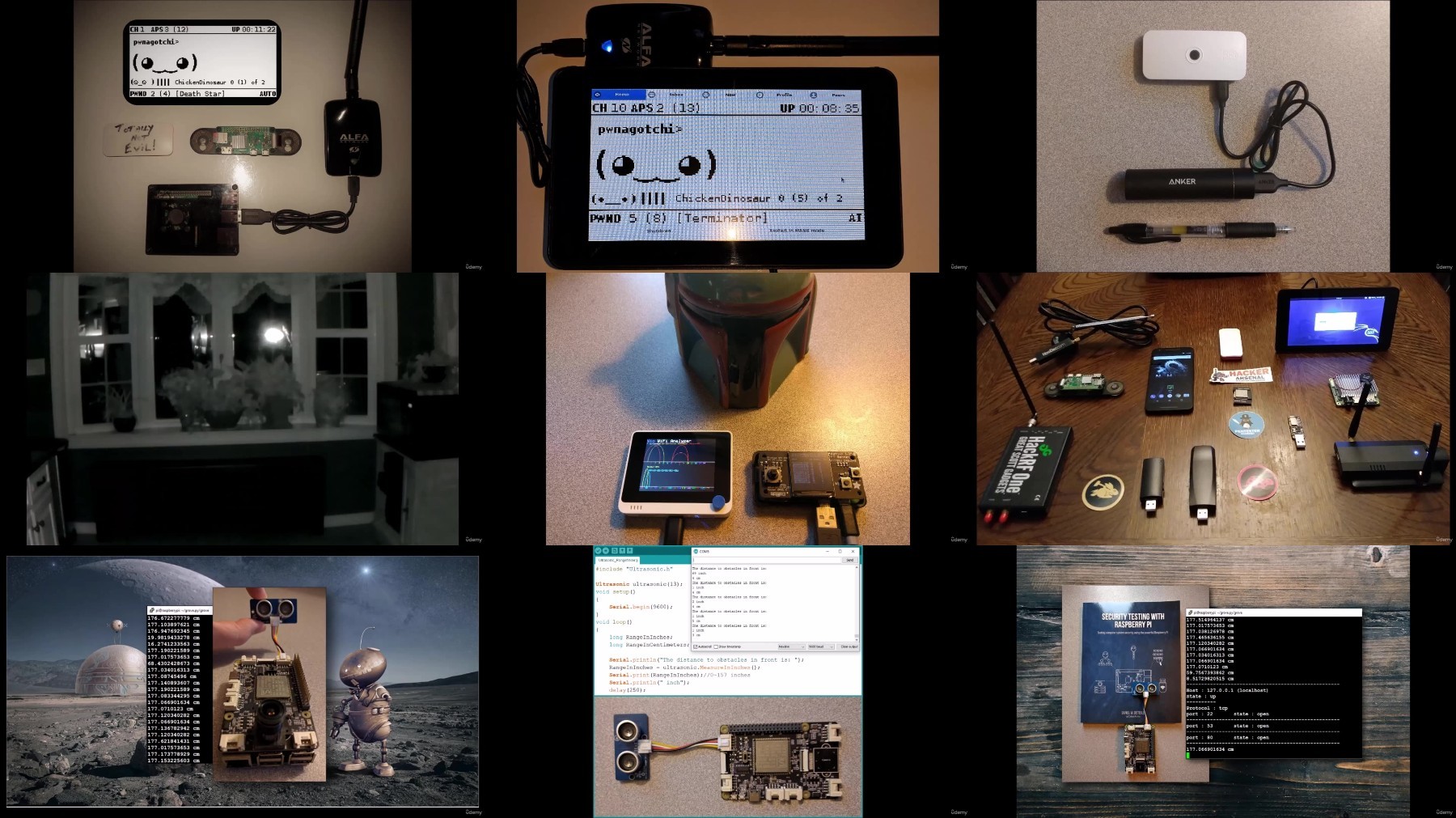
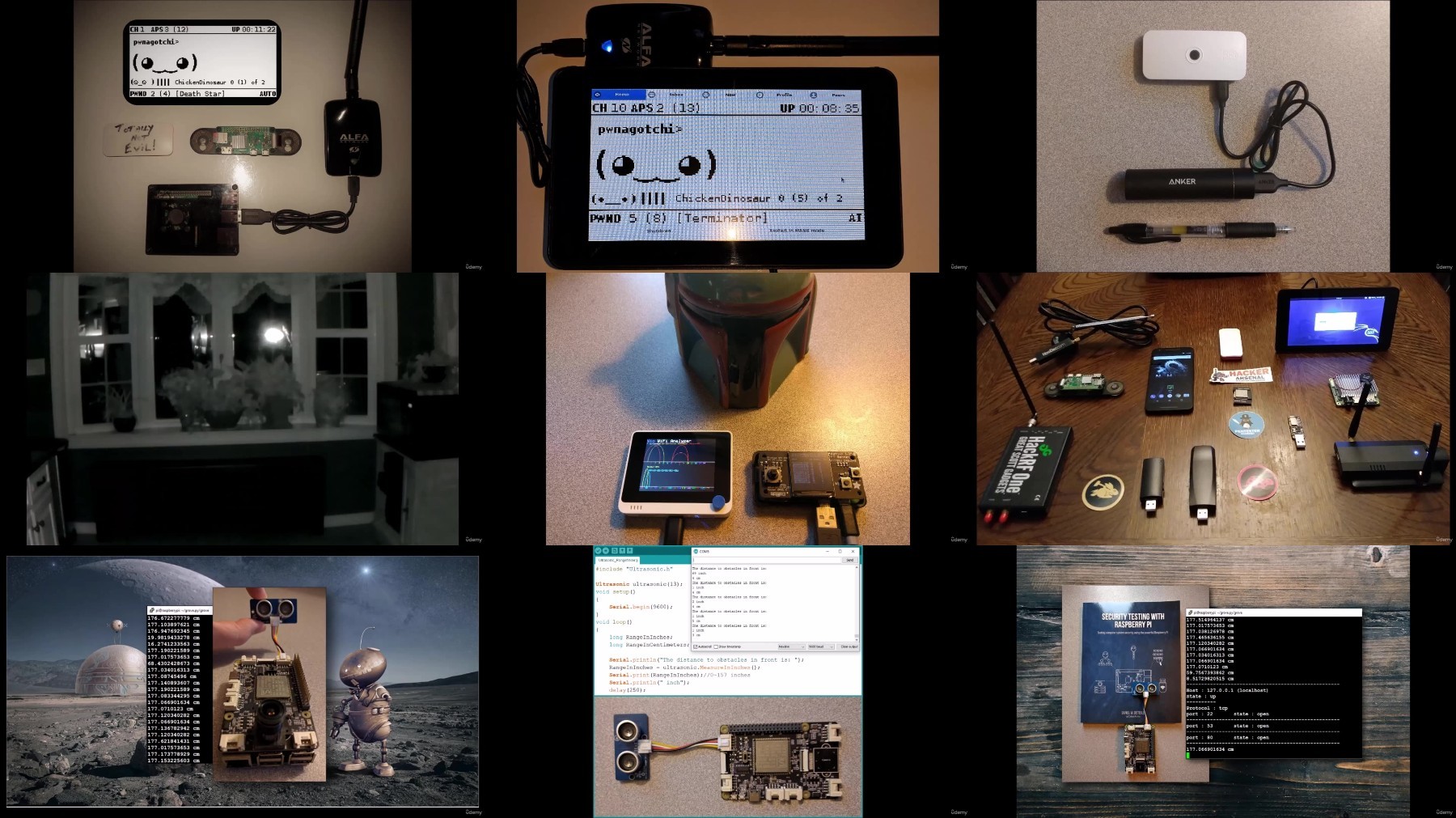
Ethical Hacking: Security Testing With Raspberry Pi




Description material

Ethical Hacking: Security Testing With Raspberry Pi
Published 1/2024
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Size: 1.56 GB | Duration: 1h 25m
Weaponizing Your Raspberry Pi - Red Team, Pentesting and Ethical Hacking with Kali Linux and Raspberry Pi!
What you'll learn
Use Raspberry Pis for Pentesting, Red Team and Ethical Hacking
Perform Network Security Scans using Raspberry Pi and Kali Linux
Learn how to Perform Wi-Fi Scans and Attacks
See How to Build Your Own Pentesting Platforms on Raspberry Pi
Requirements
This is a Step-by-Step learning series, but it would be best to have basic Linux usage and networking experience, also familiarity with a raspberry Pi is highly recommended but not necessary.
Description
Welcome to "Security Testing with Raspberry Pi," an innovative course meticulously crafted for the modern cybersecurity professional. In this dynamic program, we'll not only explore the basics of ethical hacking using Kali Linux and Raspberry Pi but also delve into advanced techniques, including Software Defined Radio (SDR), and the creation of custom platforms.Portability and AccessibilityOne of the key advantages of Kali Linux on a Raspberry Pi is portability. The Raspberry Pi's small form factor makes it an ideal platform for on-the-go ethical hacking. Whether you're conducting security assessments in diverse environments or performing Red Team building penetration tests, the Raspberry Pi allows you to carry your hacking toolkit in your pocket.Course Overview: Embark on a comprehensive journey as we unlock the potential of Kali Linux, strategically implement offensive security practices, and exploit vulnerabilities responsibly. Beyond the basics, this course pushes the boundaries by integrating cutting-edge technologies, ensuring you're well-equipped to face the challenges of contemporary cybersecurity.Key Highlights:Kali Linux: Uncover using Kali Linux on a Raspberry Pi, exploring its powerful penetration testing tools and mastering the art of ethical hacking.Offensive Security Techniques: Proactively identify, exploit, and secure systems, gaining hands-on experience in offensive security tools.Penetration Testing Essentials: Develop expertise in Reconnaissance, Scanning, Exploitation, and Wireless Security, essential for effective penetration testing.Raspberry Pi Integration: Harness the compact yet powerful Raspberry Pi as a platform for ethical hacking, creating your portable toolkit for on-the-go security assessments.Software Defined Radio (SDR): Explore the realm of using SDR on a Pi using DragonOS.Pentest Drop Boxes: Kali on a Pi is the perfect solution for deploying and utilizing pentest drop boxes, enabling remote testing and assessment of target environments.Building Custom Platforms: Elevate your skills by building custom platforms tailored to specific ethical hacking needs, ensuring adaptability to diverse scenarios.Who Should Enroll: This course caters to computer science professionals, IT administrators, and cybersecurity enthusiasts seeking to advance their skills in ethical hacking. Whether you're an experienced practitioner or a beginner, this class offers a hands-on learning experience that goes beyond conventional boundaries.Join us on this thrilling journey of ethical hacking with Kali Linux, Raspberry Pi, SDR, and the tools of tomorrow. Let's fortify the digital landscape together!Disclaimer: This is an Ethical Hacking course. Always practice training in a test lab environment. Never use the techniques shown here to test, access or attack a system that you do not have permission to access. Doing so is illegal, and you could go to jail. This course is for informational purposes only.
Overview
Section 1: Introduction
Lecture 1 Introduction: Weaponizing your Raspberry Pi
Section 2: Installing Kali Linux on Raspberry Pi
Lecture 2 Installing Kali Linux
Section 3: Basic Network Scanning
Lecture 3 Using NMAP to Perform Basic Network Scans
Lecture 4 Network Recon with Reconnoitre
Section 4: Performing Web Application Security Scans
Lecture 5 Scanning Web Apps for Vulnerabilities with Wapiti3
Lecture 6 Testing Web App Security with Sniper
Section 5: Testing Wireless Security (Scans and Attacks) using Raspberry Pi
Lecture 7 WiFi Scans: Getting the Lay of the Land with Airodump-NG
Lecture 8 WiFi Security Tests: Using BetterCap
Lecture 9 WiFi Attacks: Cracking WPA Network Keys with Fern WiFi Cracker
Lecture 10 Attacking Air Gapped Networks with P4wnP1 ALOA
Section 6: Command & Control (C2) with a Raspberry Pi
Lecture 11 C2: Command and Control with StarKiller Empire
Lecture 12 C2: Using PoshC2 for Command & Control
Section 7: Roll your Own Hacking Platform, SDR & Future Uses of Raspberry Pis in Security
Lecture 13 PiOS, Pentesters FrameWork, SDR with Dragon OS, Ubuntu on the Pi
Lecture 14 Future Uses of Raspberry Pi in Security
This course is for both those new to Pentesting and Ethical Hacking and experienced Pentesters and Red Team members who want to expand their toolkit with Raspberry Pi

What you'll learn
Use Raspberry Pis for Pentesting, Red Team and Ethical Hacking
Perform Network Security Scans using Raspberry Pi and Kali Linux
Learn how to Perform Wi-Fi Scans and Attacks
See How to Build Your Own Pentesting Platforms on Raspberry Pi
Requirements
This is a Step-by-Step learning series, but it would be best to have basic Linux usage and networking experience, also familiarity with a raspberry Pi is highly recommended but not necessary.
Description
Welcome to "Security Testing with Raspberry Pi," an innovative course meticulously crafted for the modern cybersecurity professional. In this dynamic program, we'll not only explore the basics of ethical hacking using Kali Linux and Raspberry Pi but also delve into advanced techniques, including Software Defined Radio (SDR), and the creation of custom platforms.Portability and AccessibilityOne of the key advantages of Kali Linux on a Raspberry Pi is portability. The Raspberry Pi's small form factor makes it an ideal platform for on-the-go ethical hacking. Whether you're conducting security assessments in diverse environments or performing Red Team building penetration tests, the Raspberry Pi allows you to carry your hacking toolkit in your pocket.Course Overview: Embark on a comprehensive journey as we unlock the potential of Kali Linux, strategically implement offensive security practices, and exploit vulnerabilities responsibly. Beyond the basics, this course pushes the boundaries by integrating cutting-edge technologies, ensuring you're well-equipped to face the challenges of contemporary cybersecurity.Key Highlights:Kali Linux: Uncover using Kali Linux on a Raspberry Pi, exploring its powerful penetration testing tools and mastering the art of ethical hacking.Offensive Security Techniques: Proactively identify, exploit, and secure systems, gaining hands-on experience in offensive security tools.Penetration Testing Essentials: Develop expertise in Reconnaissance, Scanning, Exploitation, and Wireless Security, essential for effective penetration testing.Raspberry Pi Integration: Harness the compact yet powerful Raspberry Pi as a platform for ethical hacking, creating your portable toolkit for on-the-go security assessments.Software Defined Radio (SDR): Explore the realm of using SDR on a Pi using DragonOS.Pentest Drop Boxes: Kali on a Pi is the perfect solution for deploying and utilizing pentest drop boxes, enabling remote testing and assessment of target environments.Building Custom Platforms: Elevate your skills by building custom platforms tailored to specific ethical hacking needs, ensuring adaptability to diverse scenarios.Who Should Enroll: This course caters to computer science professionals, IT administrators, and cybersecurity enthusiasts seeking to advance their skills in ethical hacking. Whether you're an experienced practitioner or a beginner, this class offers a hands-on learning experience that goes beyond conventional boundaries.Join us on this thrilling journey of ethical hacking with Kali Linux, Raspberry Pi, SDR, and the tools of tomorrow. Let's fortify the digital landscape together!Disclaimer: This is an Ethical Hacking course. Always practice training in a test lab environment. Never use the techniques shown here to test, access or attack a system that you do not have permission to access. Doing so is illegal, and you could go to jail. This course is for informational purposes only.
Overview
Section 1: Introduction
Lecture 1 Introduction: Weaponizing your Raspberry Pi
Section 2: Installing Kali Linux on Raspberry Pi
Lecture 2 Installing Kali Linux
Section 3: Basic Network Scanning
Lecture 3 Using NMAP to Perform Basic Network Scans
Lecture 4 Network Recon with Reconnoitre
Section 4: Performing Web Application Security Scans
Lecture 5 Scanning Web Apps for Vulnerabilities with Wapiti3
Lecture 6 Testing Web App Security with Sniper
Section 5: Testing Wireless Security (Scans and Attacks) using Raspberry Pi
Lecture 7 WiFi Scans: Getting the Lay of the Land with Airodump-NG
Lecture 8 WiFi Security Tests: Using BetterCap
Lecture 9 WiFi Attacks: Cracking WPA Network Keys with Fern WiFi Cracker
Lecture 10 Attacking Air Gapped Networks with P4wnP1 ALOA
Section 6: Command & Control (C2) with a Raspberry Pi
Lecture 11 C2: Command and Control with StarKiller Empire
Lecture 12 C2: Using PoshC2 for Command & Control
Section 7: Roll your Own Hacking Platform, SDR & Future Uses of Raspberry Pis in Security
Lecture 13 PiOS, Pentesters FrameWork, SDR with Dragon OS, Ubuntu on the Pi
Lecture 14 Future Uses of Raspberry Pi in Security
This course is for both those new to Pentesting and Ethical Hacking and experienced Pentesters and Red Team members who want to expand their toolkit with Raspberry Pi

Join to our telegram Group
Information
Users of Guests are not allowed to comment this publication.
Users of Guests are not allowed to comment this publication.
Choose Site Language
Recommended news
Commented


![eM Client Pro 9.2.1735 Multilingual [Updated]](https://pikky.net/medium/wXgc.png)



![[PORTABLE] Coolmuster Android Backup Manager 2.2.28](https://i.postimg.cc/254r46mW/Coolmuster-Android-Backup-Manager.png)

![Movavi Video Editor 24.0.2.0 Multilingual [ Updated]](https://pikky.net/medium/qhrc.png)

