Most Commented
The Complete Web Penetration Testing & Bug Bounty Course




Description material
The Complete Web Penetration Testing & Bug Bounty Course
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 44100 Hz, 2ch | Size: 6.07 GB
Genre: eLearning Video | Duration: 102 lectures (12 hour, 41 mins) | Language: English
Learn Web Pentesting & Bug Bounty & Burpsuite by hands on experience with latest technology and a full curriculum
What you'll learn
Web Application & Website Penetration Tests
Burpsuite
Bug Bounty
Cyber Security Fundamentals
Kali Linux
Web Security
Requirements
A Computer with minimum 4GB of RAM
Internet Connection
Description
Welcome to The Complete Web Penetration Testing & Bug Bounty Course
In this course we are going to start from scratch and learn how to find vulnerabilities & bugs in Websites and Web Applications. Of course we will learn this to notify the related authorities to make internet a safer place and start making money out of this process. We are going to learn how hackers find vulnerabilities, how hackers do their attacks and also how to protect ourselves against these attacks and submit these bugs to the related developers. We will never neglect theory but we will do hands-on experience practices all the time during the course. You will be hacking into vulnerable systems throughout the course.
This training is brought to you by Codestars by Rob Percival (+1.000.000 students) and Atil Samancioglu (+200.000 students). Atil teaches cyber security & programming in Udemy for more than 5 years and he also teaches mobile development in Bogazici University. If you are looking forward to be a part of the cyber security environment then you found the right course and right instructor!
You can see some of the topics that we are going to cover throughout the course below:
Web Application Pentesting
Burpsuite
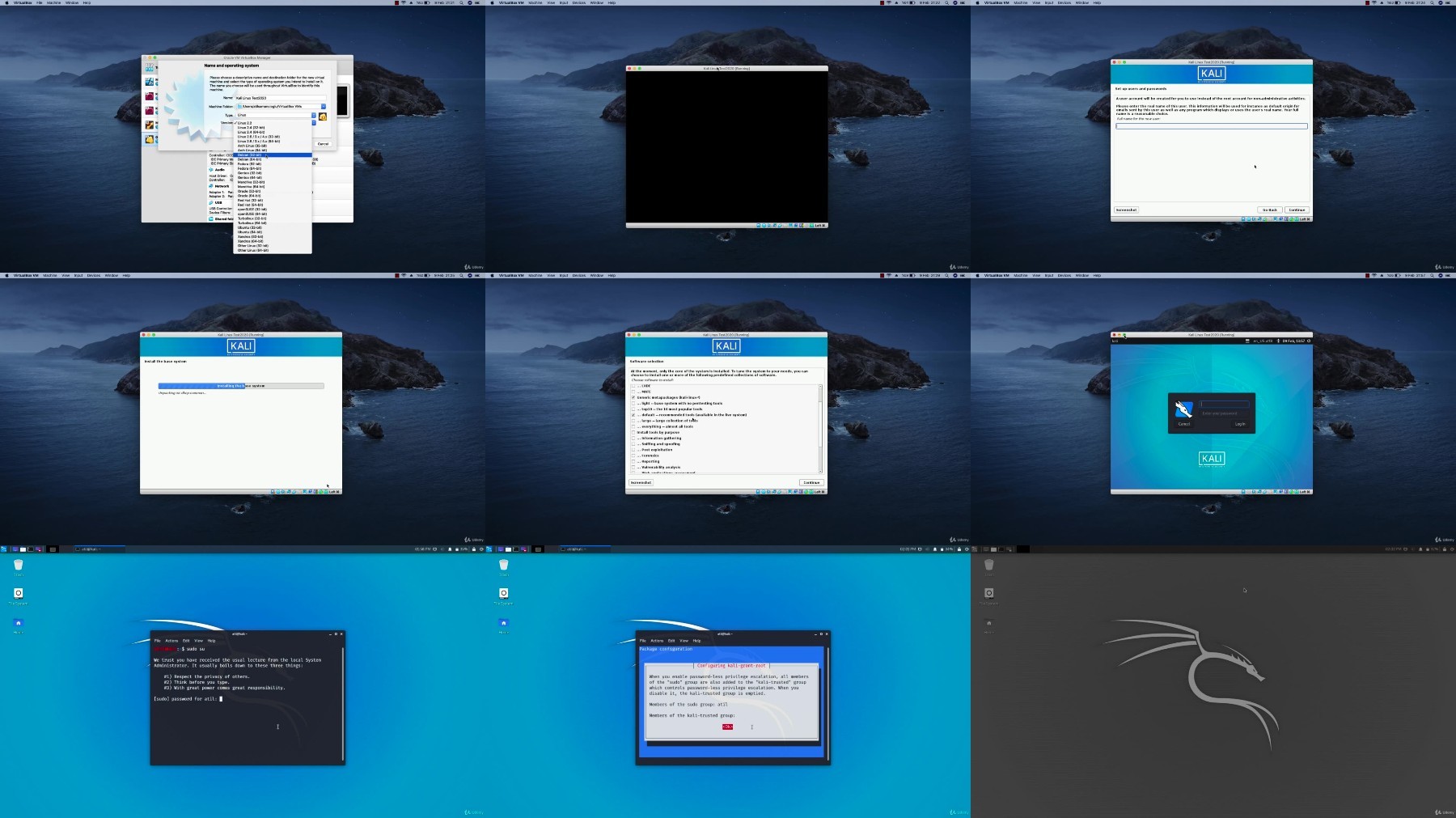
Kali Linux
HTML
bWapp
Juice Shop
Owasp Top 10
Mutillidae
DVWA
XSS
XXE
SQL Injection
HTML Injection
PHP Injection
Shell Methods
File Vulnerabilities
Nikto
Commix
Dotdotpwn
Wafw00f
Directory Traversal
Brute Force
Bug Bounty
Content
This training is perfect for people who want to be an Ethical Hacker and a Bug Bounty Hunter. We are going to start from scratch and make our way up to all details. We are going to cover Kali Linux, Burpsuite, HTML, XSS, SQL, PHP Injection and so much more. All curriculum is designed to make you comfortable during the process.
Warning: This course aims to teach people how to become ethical hackers and cyber security specialists. All students must use the related information within legal boundaries as mentioned in the course to make internet a safer place.
Who this course is for:
People who want to learn about Web Pentesting
People who want to learn making totally legal money in cyber security
People who want to learn about Burpsuite
For More Courses Visit & Bookmark Your Preferred Language Blog
From Here: - - - - - - - -
Download Links
DDownload
Warning! You are not allowed to view this text.
RapidGator
Warning! You are not allowed to view this text.
FileStore
TurboBit
Warning! You are not allowed to view this text.
FileAxa
Warning! You are not allowed to view this text.
Join to our telegram Group
Information
Users of Guests are not allowed to comment this publication.
Users of Guests are not allowed to comment this publication.
Choose Site Language
Recommended news
Commented



![eM Client Pro 9.2.1735 Multilingual [Updated]](https://pikky.net/medium/wXgc.png)





![Movavi Video Editor 24.0.2.0 Multilingual [ Updated]](https://pikky.net/medium/qhrc.png)

