Most Commented
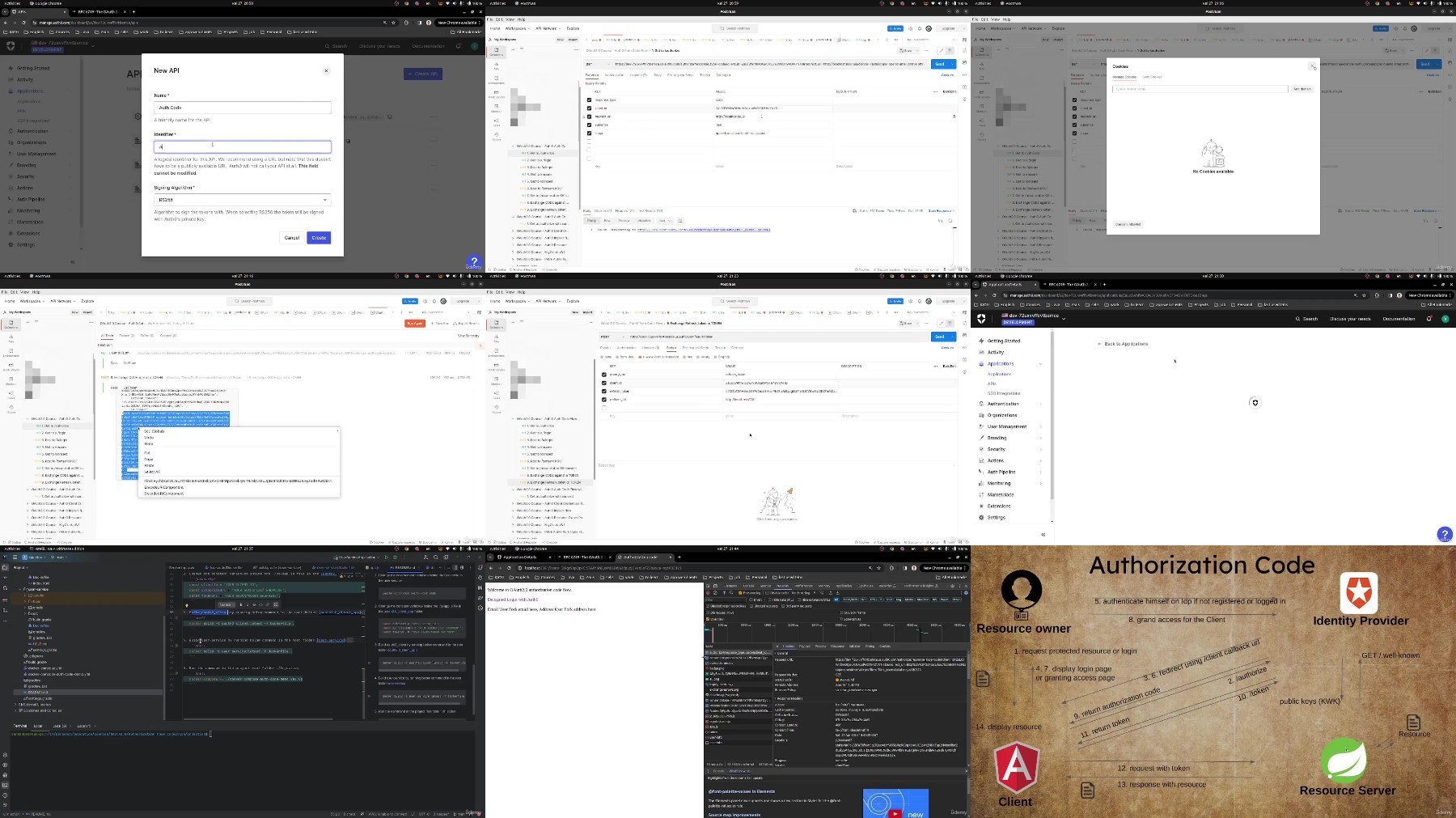
Application Security with OAuth 2.0 and OpenID Connect




Description material

Application Security with OAuth 2.0 and OpenID Connect
Published 10/2024
Duration: 4h15m | .MP4 1280x720, 30 fps(r) | AAC, 44100 Hz, 2ch | 2.07 GB
Genre: eLearning | Language: English
Learn OAuth 2/OpenID Connect, using Auth0, Postman. Use PKCE and prevent Authorization Code Injection with real example.
What you'll learn
Understand OAuth 2.0 roles and the differences between authentication and authorization frameworks
Learn the various OAuth 2.0 flows, including Resource Owner Password Credentials, Implicit, Client Credentials, and Authorization Code flows
Gain insights into advanced security topics like Authorization Code Injection and PKCE (Proof Key for Code Exchange)
Understand OIDC, the differences between access and ID tokens, and token types like JWT and opaque tokens
Apply best practices for using scopes, enhancing security, and selecting appropriate flows for different applications
Requirements
A basic understanding of web technologies and HTTP protocols
No advanced security knowledge is necessary, but having a basic understanding of APIs will be helpful.
Description
Unlock the essentials of application security with the comprehensive online course, "Getting Started with Application Security: OAuth 2.0 & OpenID." Designed for beginners and those looking to deepen their knowledge, this course equips you with the foundational principles of OAuth 2.0 and OpenID Connect.
Who should take this course?
Developers who are integrating OAuth 2.0 and OpenID Connect into their applications and need to understand both theory and practice.
IT professionals seeking to enhance their knowledge of securing API endpoints and authentication mechanisms.
Cybersecurity students or professionals wanting to learn about modern authentication techniques and security vulnerabilities.
Beginners with no prior experience in OAuth 2.0 or OpenID who want a structured and comprehensive introduction to these technologies.
What practical skills will I gain?
You'll take on the role of an attacker to simulate logging in as a regular user, while also learning how to prevent attackers from accessing user profiles and obtaining protected user data.
You'll learn how to configure different OAuth 2.0 flows, including the Authorization Code Flow, Implicit Flow, Client Credentials Flow, and more.
The course provides a deep dive into understanding and using tokens (access tokens, ID tokens, and refresh tokens).
You'll understand how to secure your applications by implementing PKCE (Proof Key for Code Exchange).
What does this course offer for you?
In-Depth Video Lessons:
Engage with clear, informative video content that breaks down complex concepts into easily digestible segments.
Practical Learning:
Go beyond theory! Practice all OAuth 2.0 flows through hands-on assignments that reinforce your understanding and skills.
Expert Insights on Security Vulnerabilities:
Learn about critical threats like Authorization Code Injection. The lesson explains how this attack works and guides you through preventive measures, ensuring you're well-prepared to safeguard applications.
Understanding Tokens:
Gain clarity on the differences between OAuth 2.0 and OpenID Connect, including a detailed overview of various token types and their roles in securing applications.
Hands-On Practice:
Master the various OAuth 2.0 flows with practical assignments that reinforce your learning and build your confidence in real-world applications.
Whether you're a developer, security enthusiast, or IT professional, this course provides valuable insights that will enhance your application security expertise. Start your journey and take the first step toward mastering OAuth 2.0 and OpenID Connect!
Who this course is for:
Developers looking to implement secure authentication and authorization in their applications using OAuth 2.0
API developers and architects who want to deepen their knowledge of secure token handling, authentication flows, and best practices.
Anyone interested in understanding modern application security with a focus on OAuth 2.0 and related standards.
More Info
DDownload
Warning! You are not allowed to view this text.
RapidGator
Warning! You are not allowed to view this text.
FileStore
TurboBit
Warning! You are not allowed to view this text.
FileAxa
Warning! You are not allowed to view this text.
Join to our telegram Group
Information
Users of Guests are not allowed to comment this publication.
Users of Guests are not allowed to comment this publication.
Choose Site Language
Recommended news
Commented



![eM Client Pro 9.2.1735 Multilingual [Updated]](https://pikky.net/medium/wXgc.png)






![Movavi Video Editor 24.0.2.0 Multilingual [ Updated]](https://pikky.net/medium/qhrc.png)

