Most Commented
Ethical Hacking & Computer NetWorks (Animated) For Beginners




Description material

Ethical Hacking & Computer Networks (Animated) For Beginners
Published 11/2024
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Size: 1.33 GB | Duration: 3h 51m
Learn Ethical hacking, Computer networks , Fundamentals of Cyber Security , Wireless hacking , Linux and more.
What you'll learn
Students Interested in Networking – Individuals who want to learn basic computer networking concepts in a fun and engaging way
Aspiring Ethical Hackers – Those who want to learn ethical hacking techniques to test and secure WiFi networks.
Professionals Seeking to Enhance Security Skills – IT professionals who want to improve their understanding of WiFi vulnerabilities and security measures.
Beginners in Cybersecurity – People new to ethical hacking or cybersecurity looking to build foundational knowledge.
Requirements
A computer with a minimum of 4GB RAM and an internet connection.
A wireless network card is needed only for wireless hacking; the other 96% of the course does not require any special equipment.
Description
The Ethical Hacking & Computer Networks (Animated) for Beginners course is designed for beginners to help you learn the basics of computer networking and WiFi hacking in an easy-to-understand way. Through engaging animations, it covers key networking concepts, such as basic terms, Network devices, Firewalls,Cryptography, TCP/IP and OSI Models and Protocols such TCP,ARP,DHCP and UDP.You will also dive deep into the world of ethical hacking, focusing specifically on WiFi networks. The course teaches you how WiFi works, how hackers exploit vulnerabilities, and how to protect against attacks. You will learn about common hacking techniques like password cracking, packet sniffing, and man-in-the-middle attacks. Step-by-step tutorials will show you how to perform these attacks in a controlled environment so you can understand the risks and defenses.This course is perfect for beginners, with no prior knowledge required. It's ideal for anyone who wants to understand how hackers think and how to secure their own network from potential threats. By the end of the course, you'll have a solid foundation in networking and ethical hacking, equipping you to protect your home or workplace WiFi network.The course emphasizes ethical hacking, meaning you will learn how to test and strengthen network security without causing harm. Throughout the lessons, you'll use legal methods to explore vulnerabilities in WiFi networks and understand how to defend against real-world attacks. The hands-on approach allows you to practice what you learn in a safe environment, making the concepts easier to grasp.By the end of the course, not only will you have gained practical skills in WiFi hacking, but you'll also understand how to secure your network against intruders. This course is great for anyone curious about cybersecurity, aspiring ethical hackers, or those who want to ensure their personal or professional networks are protected from cyber threats.
Overview
Section 1: Introduction
Lecture 1 Introduction
Section 2: Basic Terms
Lecture 2 What is a Packet?
Lecture 3 IP address explained and View your own IP address
Lecture 4 Server and types of Servers - Difference between a regular Computer & Server
Lecture 5 Client explained
Lecture 6 Host
Lecture 7 What ISP(Internet Sevice provider) and internet Connection types
Section 3: Network Topologies
Lecture 8 Introductoin to Network Topologies
Lecture 9 Bus Topology
Lecture 10 Star Topology
Lecture 11 Mesh Topology
Lecture 12 Ring and hybrid Topology
Lecture 13 Wireless Topologies
Section 4: Network Devices
Lecture 14 Ethernet Cable and Lan Port
Lecture 15 NIC - Network Interface card
Lecture 16 Mac Address - Mac vs IP
Lecture 17 Hub
Lecture 18 Switch
Lecture 19 Router
Lecture 20 Modem
Lecture 21 Repeater
Lecture 22 Wireless Access Point
Section 5: OSI Model
Lecture 23 introduction to OSI Model
Lecture 24 Application Layer
Lecture 25 Presentation Layer
Lecture 26 Transport Layer Part1
Lecture 27 Transport Layer Part 2
Lecture 28 Network Layer
Lecture 29 Data Link Layer
Lecture 30 Physical Layer
Section 6: TCP/IP Model
Lecture 31 Introduction to TCP/IP Model
Lecture 32 Why TCP-IP was Implemented NOT OSI Model
Lecture 33 OLD vs NEW TCP/IP Model
Lecture 34 Why OSI Model is Still very important if is not implemented
Lecture 35 All TCP/IP layers
Section 7: DHCP Protocol
Lecture 36 What is Dhcp protocol
Lecture 37 DHCP client and server
Lecture 38 How Dhcp works - The DORA process
Section 8: Binary Number System
Lecture 39 Introduction to Number System and types of Numebr systems used by Computers
Lecture 40 Hexadecimal and it's uses
Lecture 41 Binary to Decimal Convesion
Lecture 42 Decimal to Binary convesion
Lecture 43 Logical oprators
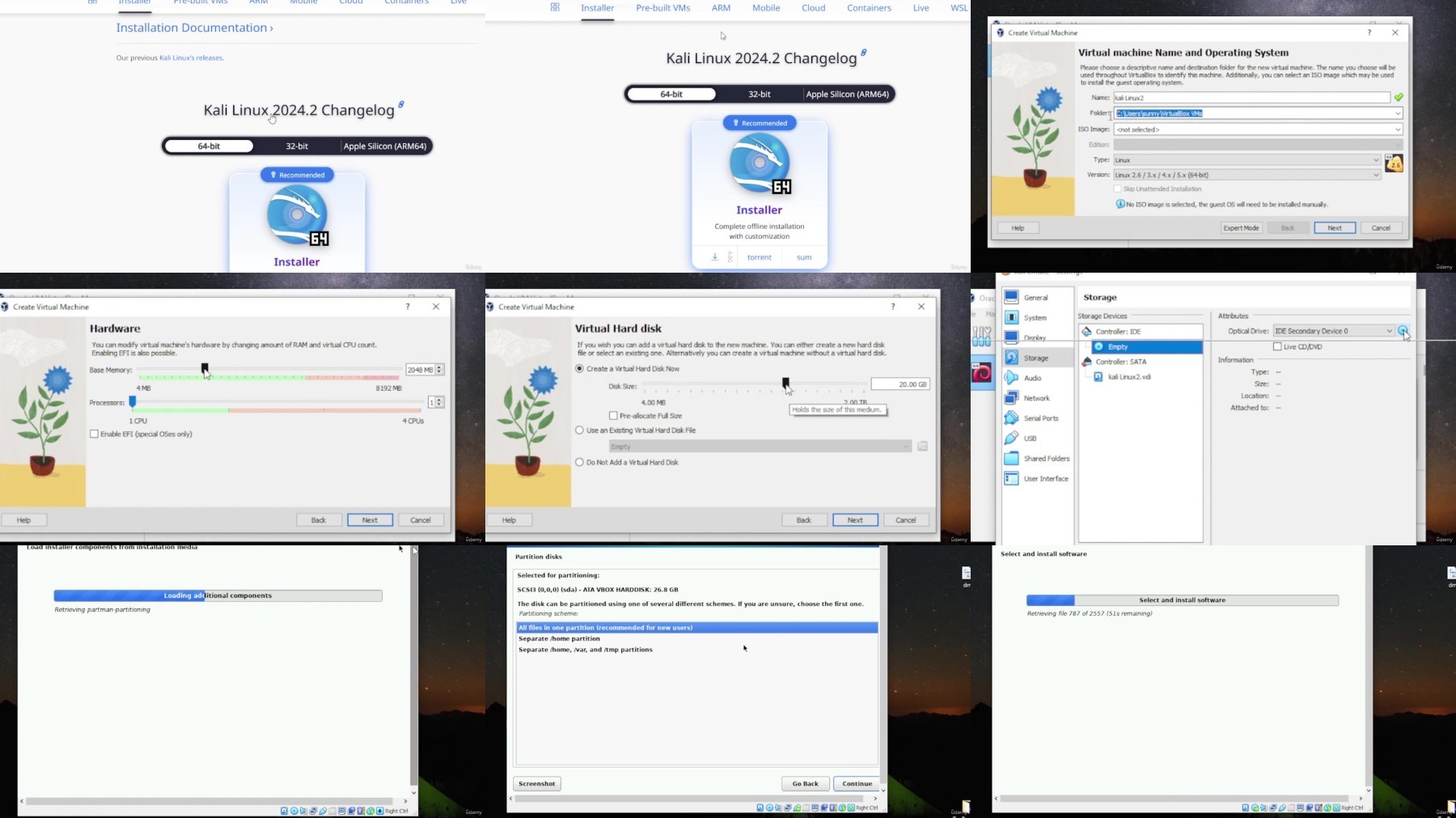
Section 9: Set up a hacking Lab
Lecture 44 Introduction to Virtual Machines
Lecture 45 Install Kali Linux
Section 10: Kali LInux Fundamentals
Lecture 46 Cd Command and essential Linux commands
Lecture 47 Ls Command
Lecture 48 Introduction to File System
Lecture 49 Introduction to Linux File System
Lecture 50 Linux Directory Structure Part1
Lecture 51 Linux Directory Structure Part2
Have no prior knowledge of Computer networks and Ethical hacking,Aspiring Ethical Hackers
FileAxa
Warning! You are not allowed to view this text.
DDownload
Warning! You are not allowed to view this text.
RapidGator
Warning! You are not allowed to view this text.
FileStore
TurboBit
Warning! You are not allowed to view this text.
Join to our telegram Group
Information
Users of Guests are not allowed to comment this publication.
Users of Guests are not allowed to comment this publication.
Choose Site Language
Recommended news
Commented



![eM Client Pro 9.2.1735 Multilingual [Updated]](https://pikky.net/medium/wXgc.png)




![[PORTABLE] Windows Movie Maker 2022 9.9.9.8 Multilingual (x64)](https://i.postimg.cc/KjfVh9Dh/Windows-Movie-Maker.png)
![Movavi Video Editor 24.0.2.0 Multilingual [ Updated]](https://pikky.net/medium/qhrc.png)

