Most Commented
Cybersecurity For Iot (Internet Of Things)




Description material

Cybersecurity For Iot (Internet Of Things)
Published 10/2024
MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz
Language: English | Size: 1.28 GB | Duration: 2h 59m
Master IoT security: Protect devices, networks, and data from cyber threats
What you'll learn
IT professionals and cybersecurity specialists looking to expand their knowledge into the growing field of IoT security
Network administrators and system engineers responsible for implementing and maintaining IoT systems in their organizations
Software developers and hardware engineers working on IoT products who want to integrate security best practices into their development process
Information security managers and CISOs seeking to understand the unique challenges and solutions in securing IoT ecosystems
Students and graduates in computer science, information technology, or cybersecurity fields interested in specializing in IoT security
IoT enthusiasts and makers who want to ensure their projects and devices are secure from potential threats
Business leaders and decision-makers who need to understand IoT security risks and mitigation strategies for their organizations
Anyone with a basic understanding of networking and cybersecurity concepts who wants to dive deep into the world of IoT security
Requirements
No prior experience with IoT security is required, but general IT or security background is helpful
Description
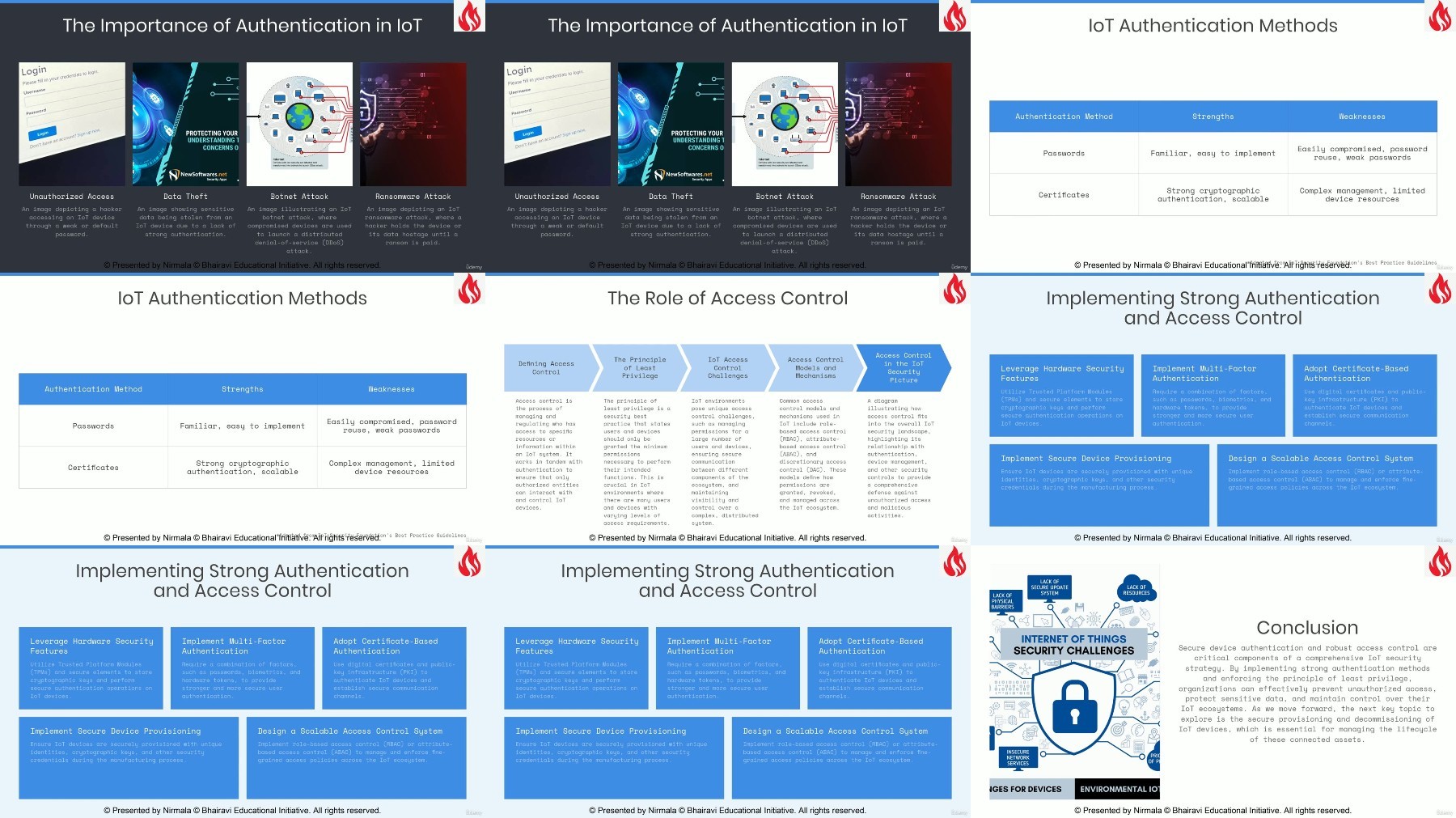
Dive into the world of IoT cybersecurity with this comprehensive course designed for IT professionals, security specialists, and IoT enthusiasts. Over seven modules, you'll gain in-depth knowledge and practical skills to secure IoT ecosystems from evolving cyber threats.Starting with the fundamentals of IoT and cybersecurity, you'll quickly progress to advanced topics such as securing IoT devices, networks, and cloud backends. Through a combination of lectures, hands-on labs, and real-world case studies, you'll learn to implement robust security measures, conduct thorough security testing, and respond effectively to IoT security incidents.Key topics covered include:IoT device security and firmware managementSecure network protocols and data encryptionCloud and backend security for IoT platformsVulnerability assessment and penetration testing for IoTImplementation of IoT security best practices and standardsIncident response and forensics in IoT environmentsBy the end of this course, you'll be equipped with the knowledge and skills to design, implement, and maintain secure IoT systems. You'll understand how to apply industry-standard frameworks like OWASP IoT Top 10 and NIST guidelines, and be prepared to tackle real-world IoT security challenges.Whether you're looking to enhance your organization's IoT security, develop secure IoT products, or advance your career in this rapidly growing field, this course provides the comprehensive training you need to succeed in IoT cybersecurity.
Overview
Section 1: Introduction
Lecture 1 Understanding the Internet of Things (IoT) Landscape
Lecture 2 IoT Devices, Sensors, and Communication Protocols
Lecture 3 The Crucial Role of Cybersecurity in IoT
Lecture 4 Common IoT Security Threats and Vulnerabilities
Lecture 5 Real-World Examples of IoT Security Breaches
Section 2: Securing IoT Devices
Lecture 6 Fundamentals of IoT Device Security
Lecture 7 Hardware Security Features for IoT Devices
Lecture 8 Firmware Updates and Patch Management Strategies
Lecture 9 Implementing Strong Device Authentication and Access Control
Lecture 10 Best Practices for Secure Device Provisioning and Decommissioning
Section 3: IoT Network and Communication Security
Lecture 11 Securing Wireless Networks in IoT Environments
Lecture 12 Encrypting and Protecting Data in Transit
Lecture 13 Securing IoT Gateways and Edge Devices
Lecture 14 Mitigating Common Network Attacks (DDoS, MITM)
Lecture 15 Hands-On Lab: Configuring Secure IoT Network Communication
Section 4: Cloud and Backend Security for IoT
Lecture 16 Securing Cloud Platforms and Services for IoT
Lecture 17 Data Protection and Encryption at Rest
Lecture 18 Designing Secure APIs and Interfaces
Lecture 19 Implementing User Authentication and Access Management
Lecture 20 Monitoring and Logging for IoT Security Incidents
Section 5: IoT Security Testing and Auditing
Lecture 21 Vulnerability Assessment and Penetration Testing for IoT
Lecture 22 Conducting Security Audits and Ensuring Compliance
Lecture 23 Developing an Effective IoT Security Testing Methodology
Lecture 24 Essential Tools for IoT Security Testing (Kali Linux, Wireshark, Nmap)
Lecture 25 Hands-On Lab: Performing IoT Security Testing
Section 6: IoT Security Best Practices and Standards
Lecture 26 Implementing OWASP IoT Top 10 Best Practices
Lecture 27 Adhering to Relevant IoT Security Standards and Frameworks (NIST SP 800-213)
Lecture 28 Integrating Security into the IoT Development Lifecycle
Lecture 29 Applying Security by Design Principles in IoT
Lecture 30 Case Studies: Learning from Real-World IoT Security Implementations
Section 7: IoT Security Incident Response and Forensics
Lecture 31 Preparing an Incident Response Plan for IoT Security Breaches
Lecture 32 Conducting IoT Forensics and Incident Investigations
Lecture 33 Implementing Containment and Recovery Strategies
Lecture 34 Lessons Learned and Continuous Improvement in IoT Security
Lecture 35 Hands-On Lab: Simulating and Responding to IoT Security Incidents
IT professionals and network administrators who want to expand their expertise into IoT security,Cybersecurity specialists looking to focus on the unique challenges of securing Internet of Things ecosystems,Software developers and hardware engineers working on IoT products who need to integrate security best practices,Information security managers and CISOs seeking to understand and address IoT-specific security risks in their organizations,Computer science and IT students with a basic understanding of networking and cybersecurity, interested in specializing in IoT security,IoT enthusiasts and makers with some technical background who want to ensure their projects are secure,Business leaders and decision-makers who need a technical understanding of IoT security for their organization's IoT implementations
FileAxa
Warning! You are not allowed to view this text.
DDownload
Warning! You are not allowed to view this text.
RapidGator
Warning! You are not allowed to view this text.
FileStore
TurboBit
Warning! You are not allowed to view this text.
Join to our telegram Group
Information
Users of Guests are not allowed to comment this publication.
Users of Guests are not allowed to comment this publication.
Choose Site Language
Recommended news
Commented



![eM Client Pro 9.2.1735 Multilingual [Updated]](https://pikky.net/medium/wXgc.png)




![[PORTABLE] GiliSoft Audio Toolbox Suite 10.0 Multilingual](https://i.postimg.cc/GmSTHcY5/Gili-Soft-Audio-Toolbox-Suite.png)
![Movavi Video Editor 24.0.2.0 Multilingual [ Updated]](https://pikky.net/medium/qhrc.png)

