Most Commented
Learn Cyberark Security




Description material

Learn Cyberark Security
Published 10/2024
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English | Size: 461.50 MB | Duration: 1h 4m
Extensive Access Control and Security Protocols
What you'll learn
Access Control Measures for Security in Cyberark
Cyberark Account related security concepts
Access Control and Safe Safe Platform in Cyberark
Cyberark Creating safe methods
Cyberark Purpose of naming conventions
Creating new safes in Cyberark
Requirements
Basic understanding of IT security concepts: Familiarity with concepts like authentication, authorization, and encryption.
Knowledge of network infrastructure: Understanding of network components, protocols, and topologies.
Description
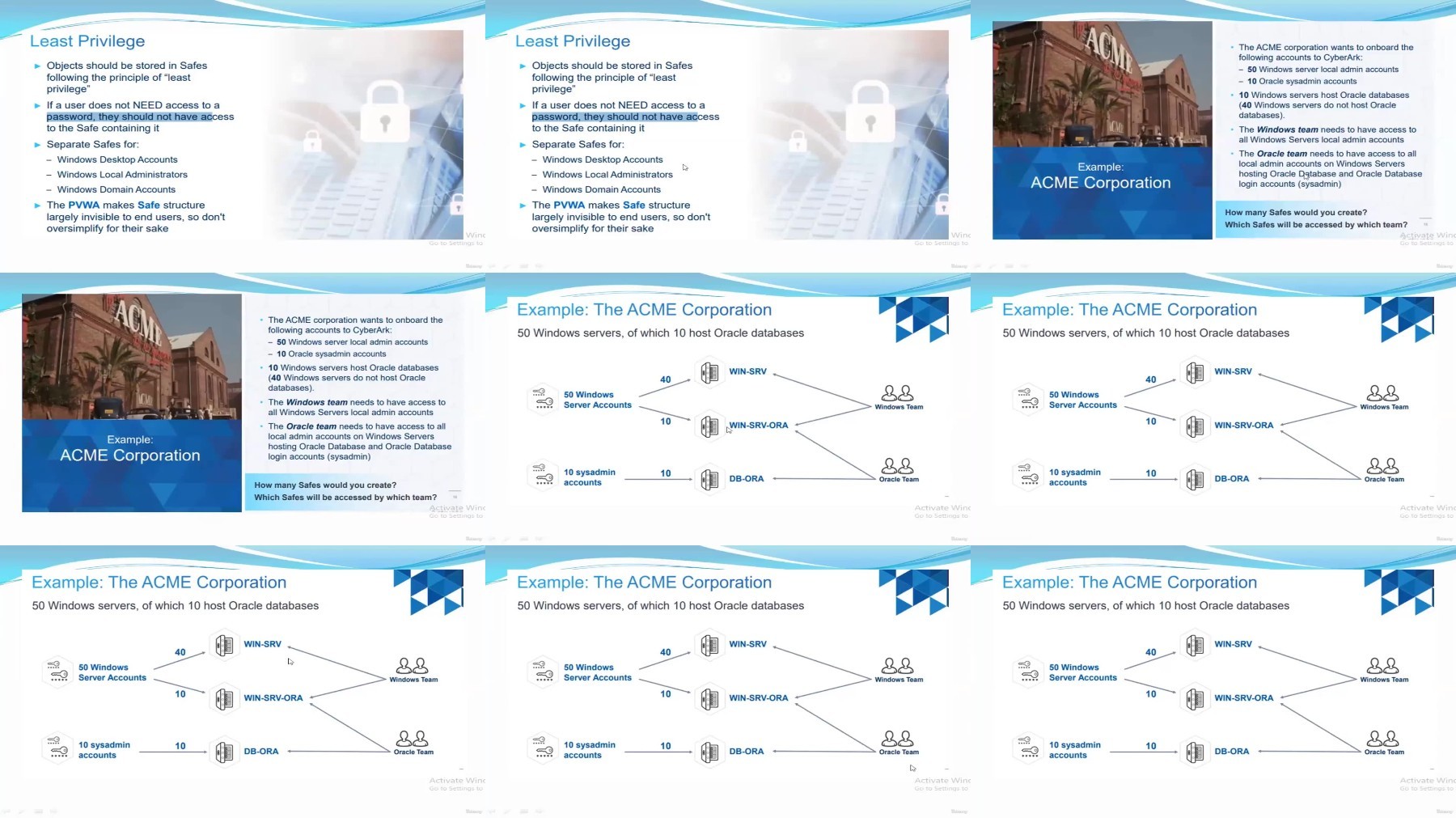
Welcome to "Learn CyberArk Security : Extensive Access Control and Security Protocols"In today's digital landscape, protecting sensitive information is more crucial than ever. This course is designed for IT professionals, security analysts, and anyone looking to deepen their understanding of CyberArk's security features and best practices.Throughout this course, you will learn how to implement robust access control measures within the CyberArk platform. We'll cover:Access Control and Safe Platform: Understand the foundational elements of CyberArk's security architecture.Account Security Concepts: Discover key principles for managing CyberArk accounts and safeguarding credentials.Creating and Managing Safes: Get hands-on experience with creating safes, establishing naming conventions, and setting up granular permissions to enhance security.Active Directory Integration: Learn how to effectively manage access through Active Directory, ensuring seamless and secure user authentication.Safe Parameters: Explore the parameters that govern safe management and configuration.By the end of this course, you will be equipped with the skills needed to effectively manage CyberArk security measures, ensuring the protection of your organization's sensitive data. Join us and take your CyberArk expertise to the next level!CyberArk helps organizations safeguard their critical assets by ensuring that only authorized users have access to sensitive data and systems.
Overview
Section 1: Cyberark Security
Lecture 1 Access Control Measures for Security in Cyberark
Lecture 2 Access Control and Safe Safe Platform in Cyberark
Lecture 3 Cyberark Account related security concepts
Lecture 4 Cyberark Creating safe methods
Lecture 5 Cyberark Purpose of naming conventions
Lecture 6 Creating new safes in Cyberark
Lecture 7 Safe granular permissions in Cyberark
Lecture 8 Active directory access in Cyberark
Lecture 9 Cyberark Safe Parameters
Security administrators,System administrators,Network engineers,Compliance officers,Anyone responsible for protecting sensitive data and systems.
FileAxa
Warning! You are not allowed to view this text.
RapidGator
Warning! You are not allowed to view this text.
FileStore
TurboBit
Warning! You are not allowed to view this text.
Join to our telegram Group
Information
Users of Guests are not allowed to comment this publication.
Users of Guests are not allowed to comment this publication.
Choose Site Language
Recommended news
Commented



![eM Client Pro 9.2.1735 Multilingual [Updated]](https://pikky.net/medium/wXgc.png)






![Movavi Video Editor 24.0.2.0 Multilingual [ Updated]](https://pikky.net/medium/qhrc.png)

